Request Information
Request Training and Certification Information, Get onsite or offsite IT Training or Testing on demand.
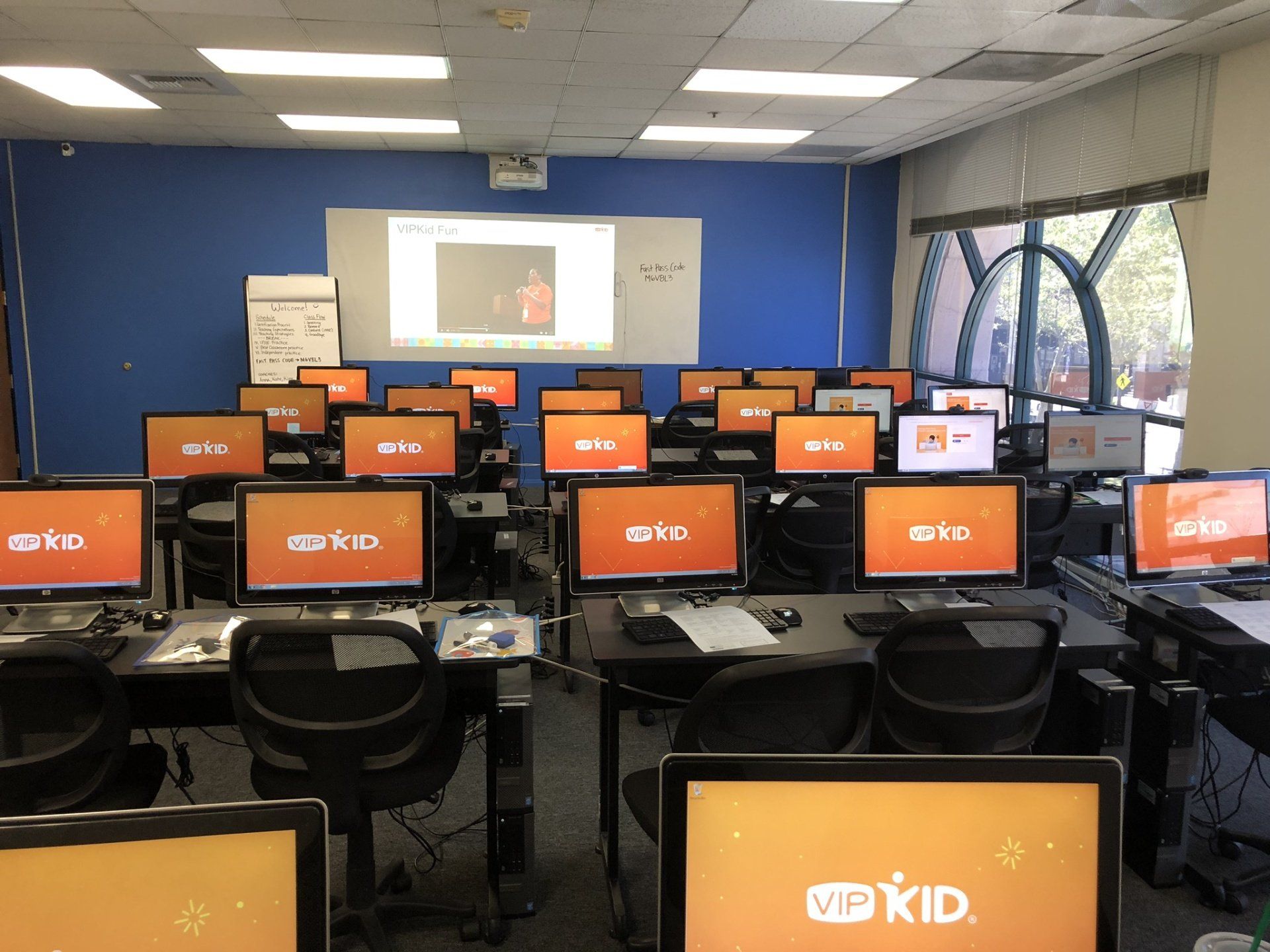
Integrated Digital Technologies (IDT) can bring the training to you or coordinate any type of training at your facility. We are equipped with a mobile classroom that can meet any companies' demand for training. We also offer training room rental and could facilitate training anywhere in the United States. IDT offers a hands-on method of training, that provides the fastest way of making sure that those trained are totally proficient in their new skills.
Please contact us for course details and schedules at 818-396-3500.
Digital Microsoft Official Curriculum
Get your books digitally at IDT
Integrated Digital Technologies (IDT) is now distributing Digital MOC for all public and private training classes. This allows our students to obtain updates and keep up to date with the technology in which they attended training. Students have 180 to view pdf files as well as download content.
As a courtesy to our students, we will print the courseware upon request. Labs and additional materials will be provided in the class to all students. Please feel free to ask any questions. Keep in mind that, you may only receive either a digital copy or a printed book since the cost to provide either material is the same to our organization. New courses are only available in a digital format.
Other vendors are also adopting this delivery, helping maintain our planet green.
Please contact us for course details and schedules at 818-396-3500.
Digital Microsoft Official Curriculum
Get your books digitally at IDT
Integrated Digital Technologies (IDT) is now distributing Digital MOC for all public and private training classes. This allows our students to obtain updates and keep up to date with the technology in which they attended training. Students have 180 to view pdf files as well as download content.
As a courtesy to our students, we will print the courseware upon request. Labs and additional materials will be provided in the class to all students. Please feel free to ask any questions. Keep in mind that, you may only receive either a digital copy or a printed book since the cost to provide either material is the same to our organization. New courses are only available in a digital format.
Other vendors are also adopting this delivery, helping maintain our planet green.
REQUEST INFO
REQUEST INFO
Thank you for contacting us.
We will get back to you as soon as possible.
We will get back to you as soon as possible.
Oops, there was an error sending your message.
Please try again later.
Please try again later.
Privacy Policy
© 2024 Integrated Digital Technologies, A Corp. All rights reserved.
Created and Designed by: Axxiom Data